Understanding WordPress Type Coercion Security for Plugin Auditing
In the dynamic landscape of web development, maintaining robust security is paramount, especially for platforms as widely used as WordPress. As we navigate 2026, one often-overlooked yet critical area of vulnerability lies within plugin code: PHP's type juggling and coercion mechanisms. This subtle yet potent threat can lead to unexpected behaviors, logic flaws, and ultimately, severe security breaches if not properly addressed during plugin development and auditing. Our project focuses on meticulously analyzing WordPress plugins to identify and mitigate such risks, providing practical insights for site owners and developers alike.
The ubiquity of WordPress means that plugins, while extending functionality, also introduce an expanded attack surface. Understanding how PHP's type juggling and coercion mechanisms can be exploited is crucial for securing a website. This article delves into the specifics of type coercion vulnerabilities, explores associated logic flaws, and outlines effective auditing strategies to safeguard your WordPress ecosystem in the current year.

Unpacking Type Coercion Vulnerabilities in WordPress Plugins
Type coercion, also known as type juggling, refers to PHP's automatic conversion of variable types based on the context of their use. While often convenient for developers, this feature can introduce significant security flaws if not handled carefully. For instance, comparing a string with a number can lead to unexpected true/false outcomes, potentially bypassing authentication checks or altering expected program flow.
Plugins often process user-supplied input, which might not always conform to the expected data type. If a plugin expects an integer but receives a string like "1abc", PHP might coerce "1abc" to 1, leading to a bypass if the check was for "not equal to 0" or similar. Attackers actively seek these discrepancies, leveraging them to manipulate application logic and gain unauthorized access.
Implicit vs. Explicit Coercion and Security Implications
- Implicit Coercion: Occurs automatically when PHP performs operations on values of different types. This is where most type coercion vulnerabilities arise because developers might not anticipate the type conversions. For example, `(string) == (int)` often evaluates to `true` under surprising conditions.
- Explicit Coercion: Involves manually casting a variable to a specific type using operators like `(int)`, `(string)`, `(bool)`. While explicit casting can prevent implicit coercion issues, incorrect usage or insufficient validation before casting can still introduce vulnerabilities.
Understanding the nuances of both implicit and explicit coercion is fundamental to identifying where a plugin might be vulnerable. Robust input validation and strict type checking are essential defenses against these subtle attacks. For more technical details on how such comparisons behave, consulting the official PHP documentation is highly recommended.
Common Scenarios Leading to Type Coercion Exploits
Several common programming patterns in WordPress plugins can lead to type coercion vulnerabilities. These often involve comparison operations, especially loose comparisons (`==` instead of `===`), or scenarios where functions expect specific types but receive others.
- Loose Comparison Operators: Using `==` instead of `===` is a frequent culprit. `0 == 'admin'` evaluates to `true`, potentially allowing an attacker to bypass checks expecting a non-numeric string username.
- Hash Comparison Issues: When comparing hashes, especially in authentication tokens or password resets, if the hash comparison is done loosely, an attacker might provide a non-string value that coerces to `0`, matching an empty hash.
- Database Queries: If values used in SQL queries are not strictly typed or properly sanitized, type coercion can lead to unexpected query execution paths, possibly allowing SQL injection or data manipulation, directly impacting secure data model integrity.
- Numerical Operations: Performing mathematical operations on user-supplied strings that could be coerced into unexpected numbers can lead to logic errors or resource exhaustion.
Each of these scenarios presents an opportunity for an attacker to manipulate the intended logic of a plugin, highlighting the critical importance of secure coding practices and vigilant auditing for WordPress Type Coercion Security.
The Evolving Landscape of WordPress Type Coercion Security in 2026
As we move through 2026, the methodologies for identifying and exploiting type coercion vulnerabilities continue to evolve. Attackers are becoming more sophisticated, leveraging automated tools and deep understanding of PHP's internal mechanisms to pinpoint weaknesses in popular WordPress plugins. This makes proactive security measures and continuous auditing more vital than ever.
Organizations and individual developers are increasingly recognizing these subtle flaws. Security researchers regularly publish advisories detailing new methods of exploitation, pushing the community to adopt stricter coding standards and comprehensive testing methodologies. Staying informed about these trends is key to maintaining a secure WordPress environment.
Recent Exploits and Case Studies
In the past year, several high-profile WordPress plugins have been found to contain type coercion vulnerabilities, leading to various impacts including authentication bypasses and sensitive data exposure. For example, a popular e-commerce plugin had a flaw where an order ID could be manipulated using a non-numeric string, leading to access to other users' order details. Similarly, an analytics plugin exhibited a type juggling issue in its API endpoint, allowing unauthenticated users to inject specific data points.
These real-world examples underscore that WordPress Type Coercion Security isn't just a theoretical concern; it's a tangible threat that requires immediate attention. Each incident serves as a crucial learning opportunity for developers to fortify their code against similar attacks.
Tooling and Techniques for Detection
Fortunately, the security community has developed an array of tools and techniques to help detect type coercion vulnerabilities. Static Application Security Testing (SAST) tools can analyze source code without execution, flagging potential type juggling issues. Dynamic Application Security Testing (DAST) tools, on the other hand, test the running application by providing varied inputs and observing responses.
Manual code review remains invaluable, especially for nuanced logic flaws that automated tools might miss. Furthermore, fuzzing – providing unexpected or malformed inputs to an application – can uncover edge cases where type coercion might be exploited. Combining these methods offers the most comprehensive approach to identifying and addressing WordPress Type Coercion Security flaws.
Beyond Coercion: Uncovering Logic Flaws in Plugin Code
While type coercion is a specific type of vulnerability, it often serves as a gateway to broader logic flaws. Logic flaws are errors in the design or implementation of an application that allow an attacker to bypass security controls or achieve unintended outcomes. These are particularly insidious because they leverage the application's intended functionality in an unintended way, making them hard to detect with typical vulnerability scanners. This is also where covert inter-plugin interactions can introduce unexpected security blindsides.
A logic flaw might involve an authentication system that correctly checks credentials but allows access if a specific, unexpected sequence of requests is made. Or, it could be a shopping cart that can be manipulated to change item prices by altering a hidden field. These flaws require a deep understanding of the plugin's business logic and user flow.
Authentication and Authorization Bypass Risks
Many critical logic flaws manifest as authentication or authorization bypasses. An attacker might exploit a type coercion vulnerability to bypass a login page, gaining administrator access. Alternatively, a design flaw might allow a lower-privileged user to access functionalities reserved for higher-privileged roles by directly accessing specific URLs or manipulating parameters.
For example, if a plugin checks user roles based on an ID, and a type coercion flaw allows an unprivileged user to pass an ID that loosely matches an administrator's, an authorization bypass occurs. Rigorous testing of all authentication and authorization paths is essential to prevent such risks.
Business Logic Vulnerabilities
Business logic vulnerabilities are design flaws specific to the application's unique processes. In WordPress plugins, this could mean flaws in how an e-commerce plugin handles payment processing, how a membership plugin manages subscriptions, or how a booking plugin allocates resources. These are highly specific and often require a manual, in-depth understanding of the plugin's intended functionality.
An example might be a coupon code system that allows unlimited uses by manipulating the session, or a donation plugin that processes negative amounts. Identifying these requires "thinking like an attacker" and understanding the specific domain of the plugin. The OWASP Top 10 often highlights such general application logic issues, emphasizing their impact on application security.
Auditing Strategies for Robust WordPress Type Coercion Security
Effectively auditing WordPress plugins for type coercion and logic flaws requires a multi-faceted approach. It involves a combination of automated tools and diligent manual review, coupled with a deep understanding of PHP's behavior and common security pitfalls. For WordPress site owners and developers in 2026, investing time and resources into a comprehensive plugin auditing strategy is non-negotiable for maintaining a secure platform.

Manual Code Review Best Practices
Manual code review is arguably the most effective method for uncovering subtle logic flaws and specific type coercion issues. It demands an experienced reviewer who can meticulously examine the plugin's source code, line by line, looking for:
- Usage of loose comparison operators (`==`, `!=`) instead of strict ones (`===`, `!==`).
- Input validation weaknesses, especially where user-supplied data is not explicitly cast or validated for type before use.
- Functions that handle sensitive data (e.g., authentication, authorization, financial transactions) where type juggling could lead to bypasses.
- Complex conditional statements where unexpected type coercion might alter the flow of execution.
- Any areas where PHP's automatic type conversion might conflict with the developer's intent.
Pair programming or having multiple reviewers examine critical sections of code can significantly enhance the effectiveness of manual auditing, catching issues related to WordPress Type Coercion Security that a single person might overlook, and helping to strengthen code against tampering.
Automated Static Analysis and Dynamic Testing
While manual review is thorough, it can be time-consuming. Automated tools play a crucial role in scaling security efforts. Static Application Security Testing (SAST) tools can scan plugin source code without executing it, identifying common coding vulnerabilities, including some type coercion patterns. These tools are excellent for catching obvious errors and enforcing coding standards.
Dynamic Application Security Testing (DAST) tools, on the other hand, test the running application. They simulate attacks by sending various inputs to the plugin and observing its behavior. Fuzzing, a technique where automated tools send large amounts of semi-random data to the plugin's inputs, can be particularly effective at uncovering unexpected type coercion behaviors that lead to crashes or security bypasses. Both SAST and DAST, when used in conjunction, provide a robust layer of defense against vulnerabilities, including those related to WordPress Type Coercion Security.
Utilizing tools like PHPStan, Psalm, or more specialized security scanners designed for PHP can greatly assist in this process, highlighting potential issues before they become exploitable. Many continuous integration/continuous deployment (CI/CD) pipelines in 2026 integrate these tools to ensure security checks are part of every code commit.
Supply Chain Security for WordPress Plugins
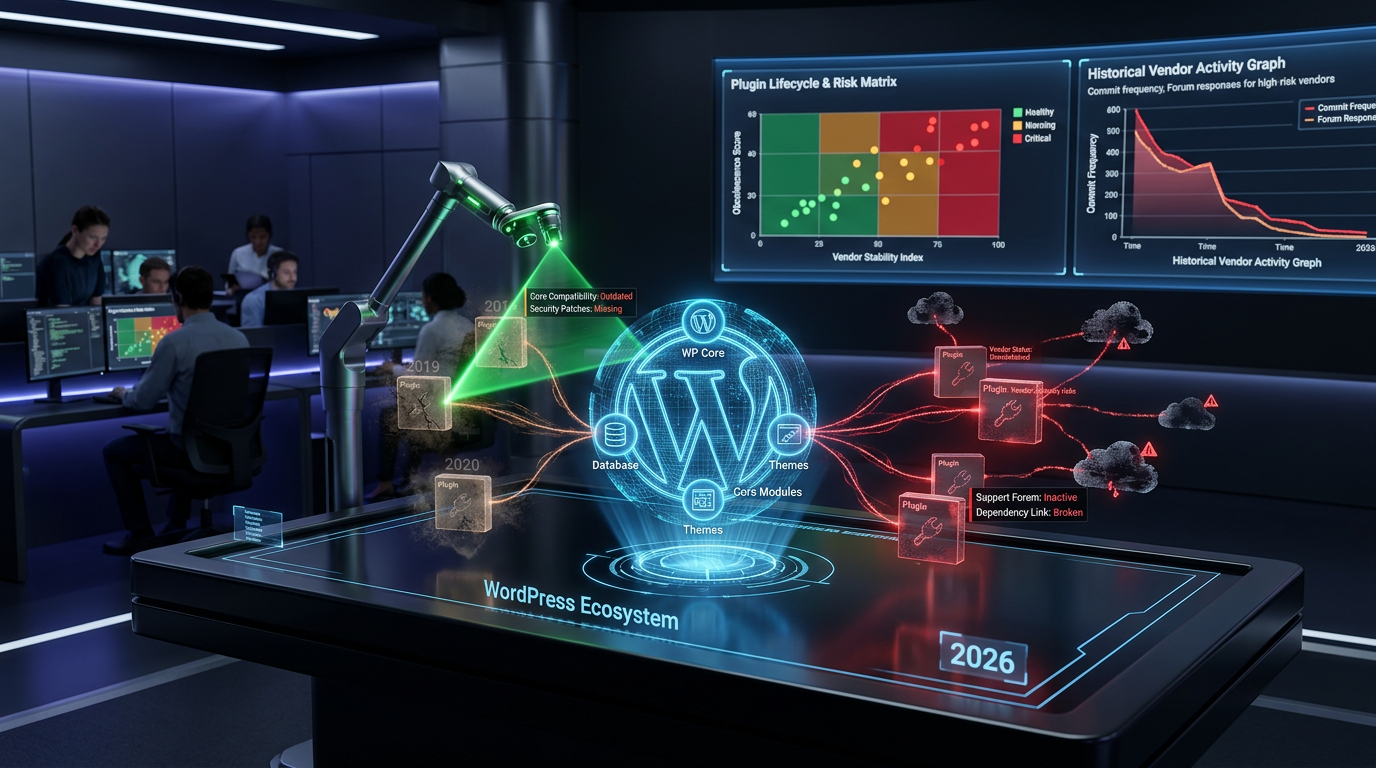
Beyond auditing your own code or the plugins you directly use, considering the broader supply chain is increasingly important. Many WordPress plugins rely on third-party libraries or frameworks, which themselves can harbor vulnerabilities, including type coercion issues. Auditing these dependencies is crucial.
Site owners should prioritize plugins from reputable developers with a strong track record of security. Regularly updating plugins is also a key aspect of supply chain security, as updates often include patches for newly discovered vulnerabilities. Subscribing to security advisories and maintaining an inventory of all plugins and their dependencies ensures that you are aware of potential risks. OWASP's guidance on Supply Chain Risk Management offers valuable principles that apply directly to the WordPress plugin ecosystem.
Conclusion: Fortifying WordPress Type Coercion Security in 2026
The security landscape for WordPress continues to evolve, making the detailed examination of plugin code more critical than ever in 2026. WordPress Type Coercion Security, along with broader logic flaws, represents a significant vector for attack that demands vigilance from both plugin developers and site administrators. By understanding the mechanics of type coercion, staying informed about current threats, and implementing rigorous auditing strategies, we can collectively build a more resilient and secure WordPress ecosystem.
Prioritizing secure coding practices, embracing comprehensive testing methodologies including manual code reviews and automated tools, and focusing on the entire plugin supply chain are the pillars of a strong security posture. Continuous education and proactive defense are not just best practices; they are essential for protecting millions of WordPress sites from the subtle yet devastating impacts of type coercion and logic flaws.
Frequently Asked Questions

Written by Aras Akıncılar
Uzun yıllara dayanan WordPress deneyimine sahip bir siber güvenlik uzmanı olarak, eklenti ekosisteminin derinlemesine analizine odaklanıyorum. Güvenlik açıkları, performans düşüşleri ve uyumluluk sorunları üzerine hazırladığım makalelerle, WordPress kullanıcılarının sitelerini daha güvenli ve verimli hale getirmelerine yardımcı olmayı hedefliyorum.